Slack Group
Before we get started I have started a slack group dedicated to hacking. We welcome everyone from beginner to advanced to join. I will be on everyday answer questions, doing CTFs, and talking about cool hacks. If you enjoy hacking and are looking for like minded people join below:
NEW Hacking Group Slack Channel
Introduction
Almost everyone has heard of subdomain hijacking but what about broken link hijacking. These two vulnerabilities are very similar the major difference is that one involves a subdomain while the other involves an expired link on a page. Shout out to edoverflow, for explaining this technique in his blog post.
Stored XSS
Broken link hijacking can be exploited to do many things but I will be talking about how to get stored XSS from expired links. The concept is actually fairly basic.
<html>
<head>
<title>Ghostlulz - Broken Link Hijacking</title>
</head>
<body>
<script src="vulnerable.com/javascript_file.js"></script>
</body>
</html>As you can see above we have an HTML page that utilizes an external javascript file. This page is trying to import a file from “vulnerable.com”. If this website is expired an attacker could buy the domain “vulnerable.com” and host their own malicious javascript file. The target application would then import this file which could cause stored XSS.
Thats it, all we are doing is registering an expired domain and uploading a malicious javascript file. Just make sure your XSS payload is stored in the malicious javascript file and your good to go.
Broken Link Checker
Before you can take advantage of a broken link you have to find it. The following tool can be used to scan an application for broken links:
Once the tool is downloaded you can run the following command to scan an application:
blc -r –filter-level 2 https://starbucks.com | grep “\.js” | grep “BROKEN”
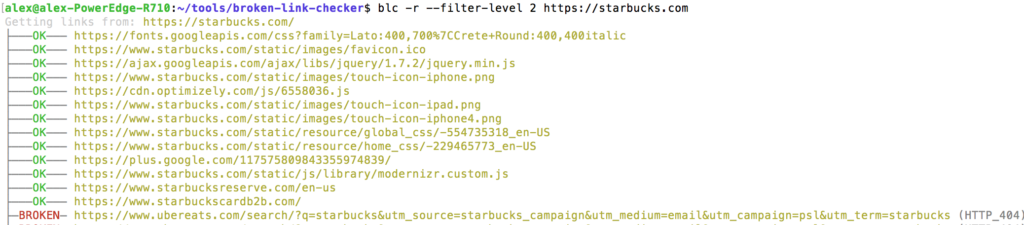
This tool will attempt to find all broken links on the page. Remember that if your looking for stored XSS you will have to find vulnerable javascript files that are being imported.
Conclusion
I always hear people talking about subdomain hijacking but I never hear anyone mentioning broken link hijacking. If you find a vulnerable javascript file you may be able to get stored XSS. Very few people know about this type of attack and even fewer are searching for it. This is the perfect recipe for easy wins.
I love looking at and I believe this website got some genuinely utilitarian stuff on it! .
Howdy! Would you mind if I share your blog with my myspace group? There’s a lot of folks that I think would really enjoy your content. Please let me know. Cheers
I noticed one of your pages have a 404 error.
Wow, this article is good, my sister is analyzing these kinds of things, so I am going to tell her.|
This is a great blog.
Does your website have a contact page? I’m having problems locating it but, I’d like to send you an e-mail. I’ve got some recommendations for your blog you might be interested in hearing. Either way, great blog and I look forward to seeing it improve over time.|
Great news once again!
I noticed one of your pages have a 404 error.
Saved as a favorite, I really like your website!|
Hello, i read your blog occasionally and i own a similar one and i was just curious if you get a lot of spam feedback? If so how do you protect against it, any plugin or anything you can suggest? I get so much lately it’s driving me insane so any assistance is very much appreciated.|
Ahaa, its nice conversation on the topic of this post at this place at this blog, I have read all that, so at this time me also commenting at this place.|
This is a great blog.
Howdy, i read your blog occasionally and i own a similar one and i was just curious if you get a lot of spam feedback? If so how do you prevent it, any plugin or anything you can suggest? I get so much lately it’s driving me insane so any help is very much appreciated.|
I will right away grab your rss feed as I can not in finding your email subscription link or e-newsletter service. Do you have any? Please permit me recognise in order that I may just subscribe. Thanks.
bookmarked!!, I love your blog!|
I love reading your site.
I noticed one of your pages have a 404 error.
It is perfect time to make some plans for the future and it’s time to be happy. I have read this post and if I could I desire to suggest you few interesting things or suggestions. Perhaps you could write next articles referring to this article. I wish to read more things about it!|
I love reading your site.
Great news once again!
Amazin!
This is a great blog.
Amazin!
It’s very easy to find out any matter on net as compared to books, as I found this article at this site.|
Woah! I’m really loving the template/theme of this site. It’s simple, yet effective. A lot of times it’s very difficult to get that “perfect balance” between superb usability and visual appeal. I must say you’ve done a fantastic job with this. Additionally, the blog loads extremely quick for me on Chrome. Outstanding Blog!|
Amazin!
Greetings from Carolina! I’m bored to tears at work so I decided to check out your website on my iphone during lunch break. I really like the information you provide here and can’t wait to take a look when I get home. I’m amazed at how quick your blog loaded on my mobile .. I’m not even using WIFI, just 3G .. Anyways, very good site!|
Great news once again!
Amazin!
This is a great blog.
Amazin!
Amazin!
Hey there just wanted to give you a quick heads up. The words in your post seem to be running off the screen in Chrome. I’m not sure if this is a format issue or something to do with browser compatibility but I figured I’d post to let you know. The style and design look great though! Hope you get the issue solved soon. Many thanks|
Great news once again!
Amazin!
Great news once again!
It’s the best time to make some plans for the future and it’s time to be happy. I have read this post and if I could I wish to suggest you few interesting things or advice. Perhaps you can write next articles referring to this article. I desire to read even more things about it!|
I noticed one of your pages have a 404 error.
Way cool! Some very valid points! I appreciate you writing this write-up and the rest of the site is really good.|
Amazin!
Howdy, I believe your blog could be having internet browser compatibility problems. Whenever I look at your blog in Safari, it looks fine however, if opening in Internet Explorer, it has some overlapping issues. I simply wanted to provide you with a quick heads up! Apart from that, great site!
Good post. I learn something new and challenging on websites I stumbleupon every day. It will always be interesting to read content from other authors and use something from their websites.
Great news once again!
This is the right website for anyone who wishes to find out about this topic. You understand so much its almost tough to argue with you (not that I personally will need to…HaHa). You definitely put a brand new spin on a topic that has been written about for decades. Wonderful stuff, just great!
I noticed one of your pages have a 404 error.
Howdy, i read your blog from time to time and i own a similar one and i was just wondering if you get a lot of spam feedback? If so how do you protect against it, any plugin or anything you can advise? I get so much lately it’s driving me crazy so any help is very much appreciated.|
Spot on with this write-up, I seriously believe that this website needs a great deal more attention. I’ll probably be back again to see more, thanks for the info!
I noticed one of your pages have a 404 error.
I love reading your site.
I noticed one of your pages have a 404 error.
Great news once again!
This is a great blog.
I love reading your site.
I love what you guys are up too. This type of clever work and exposure! Keep up the great works guys I’ve added you guys to my blogroll.|
Amazin!
Amazin!
Hi would you mind sharing which blog platform you’re working with? I’m going to start my own blog in the near future but I’m having a tough time choosing between BlogEngine/Wordpress/B2evolution and Drupal. The reason I ask is because your layout seems different then most blogs and I’m looking for something unique. P.S Sorry for getting off-topic but I had to ask!|
Everything is very open with a clear clarification of the issues. It was truly informative. Your site is very useful. Thank you for sharing!
Great news once again!
I noticed one of your pages have a 404 error.
Good post. I learn something new and challenging on websites I stumbleupon on a daily basis. It’s always exciting to read through articles from other authors and use a little something from their web sites.
Having read this I thought it was very enlightening. I appreciate you taking the time and effort to put this content together. I once again find myself spending way too much time both reading and leaving comments. But so what, it was still worth it!
I like it when folks come together and share opinions. Great site, continue the good work!|
I really like what you guys are usually up too. This kind of clever work and coverage! Keep up the amazing works guys I’ve incorporated you guys to blogroll.|
Amazin!
I noticed one of your pages have a 404 error.
I love reading your site.
Amazin!
Great news once again!
Amazin!
This is a great blog.
This is a great blog.
Way cool! Some very valid points! I appreciate you penning this write-up and also the rest of the site is very good.
I really like it whenever people get together and share ideas. Great website, keep it up!|
Great news once again!
I noticed one of your pages have a 404 error.
This is a topic that is near to my heart… Take care! Where are your contact details though?|
Spot on with this write-up, I honestly believe that this website needs a lot more attention. I’ll probably be back again to read through more, thanks for the advice!
After going over a few of the blog posts on your blog, I really like your technique of blogging. I book-marked it to my bookmark website list and will be checking back in the near future. Please check out my web site as well and tell me how you feel.
Amazin!
I noticed one of your pages have a 404 error.
This is a great blog.
Great news once again!
Greetings, I do think your web site could possibly be having internet browser compatibility issues. Whenever I look at your site in Safari, it looks fine however, when opening in IE, it’s got some overlapping issues. I merely wanted to provide you with a quick heads up! Aside from that, excellent blog!
I noticed one of your pages have a 404 error.
This is a topic which is near to my heart… Take care! Where are your contact details though?|
Having read this I believed it was very informative. I appreciate you finding the time and effort to put this short article together. I once again find myself spending a significant amount of time both reading and posting comments. But so what, it was still worthwhile!
Saved as a favorite, I like your website!
Great news once again!
That is a good tip particularly to those new to the blogosphere. Simple but very precise info?Thanks for sharing this one. A must read article!
Nice post. I learn something new and challenging on websites I stumbleupon everyday. It will always be helpful to read through articles from other authors and use something from their websites.
Amazin!
I was pretty pleased to discover this page. I wanted to thank you for your time due to this fantastic read!! I definitely really liked every part of it and i also have you saved as a favorite to see new information in your site.
I noticed one of your pages have a 404 error.
Great news once again!
Spot on with this write-up, I really believe this site needs much more attention. I’ll probably be returning to see more, thanks for the advice!
Amazin!
You ought to take part in a contest for one of the finest sites on the net. I’m going to highly recommend this blog!
Howdy! This post could not be written any better! Looking through this article reminds me of my previous roommate! He always kept talking about this. I will send this information to him. Pretty sure he’ll have a good read. Thank you for sharing!
Great news once again!
This is a great blog.
This is a very good tip especially to those fresh to the blogosphere. Brief but very precise information?Appreciate your sharing this one. A must read article!
Way cool! Some extremely valid points! I appreciate you penning this article plus the rest of the site is also really good.
Amazin!
I’m pretty pleased to find this website. I want to to thank you for your time for this fantastic read!! I definitely savored every bit of it and i also have you saved to fav to check out new information on your site.
Way cool! Some very valid points! I appreciate you writing this article and the rest of the website is also really good.|
Great news once again!
Amazin!
The very next time I read a blog, Hopefully it does not fail me just as much as this one. After all, I know it was my choice to read through, however I really believed you would have something useful to talk about. All I hear is a bunch of whining about something that you can fix if you weren’t too busy seeking attention.
After exploring a number of the blog posts on your web page, I really like your way of writing a blog. I saved as a favorite it to my bookmark website list and will be checking back in the near future. Take a look at my web site as well and let me know what you think.
Great news once again!
This is a great blog.
Saved as a favorite, I like your web site!
I love reading your site.
Howdy, I believe your web site could be having web browser compatibility problems. When I take a look at your blog in Safari, it looks fine however, when opening in I.E., it has some overlapping issues. I just wanted to provide you with a quick heads up! Apart from that, great website!
I have been surfing on-line more than three hours these days, but I by no means discovered any fascinating article like yours. It’s lovely worth enough for me. In my opinion, if all site owners and bloggers made just right content as you probably did, the internet might be a lot more helpful than ever before.|
Great news once again!
Howdy! I simply want to offer you a huge thumbs up for your excellent info you’ve got right here on this post. I’ll be returning to your blog for more soon.