Slack Group
Before we get started I have started a slack group dedicated to hacking. We welcome everyone from beginner to advanced to join. I will be on everyday answer questions, doing CTFs, and talking about cool hacks. If you enjoy hacking and are looking for like minded people join below:
NEW Hacking Group Slack Channel
Introduction
Log and configuration files are used by applications to store error messages, warning messages, startup variables, and other things. These files can contain sensitive information such as passwords, encryption keys, tokens, and anything else you would want as an attacker. For applications that are not exposed to the internet this may not be a problem as no one would have access to the sensitive data but web applications are exposed to the internet.
Exposed Files
The only way to find exposed log and configuration files on an application is to know the file name. The best way to find these files is to create a list of common files and perform directory brute forcing. Some common log file names include:
- logs.txt
- log.txt
- debug.log
- *.log
- *.config
- etc
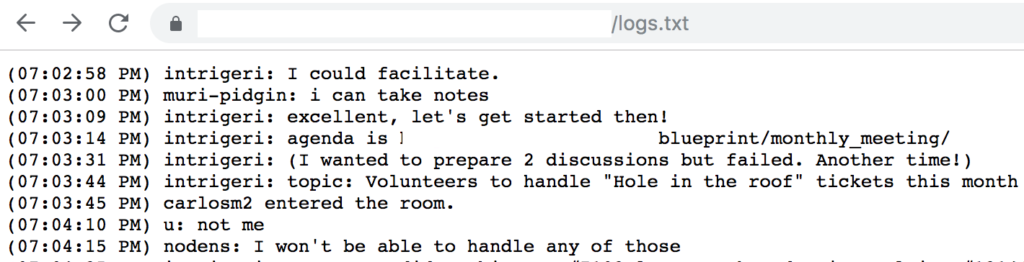
You may be able to come up with a fairly good list of possible file names but a lot of application and frameworks name their files something like “juio_life-framework.log” which is not easily guessable. The only way to find these files is to understand what each technology stack and framework names their log and configuration files. There are thousands of different frameworks so I obviously can’t talk about each one of them but ill go over a few so you get the idea.
Global.asa
The global.asa configuration file is used by ASP.net applications to store information and objects used by the application. These essential act as global variables. This file is typically stored in the root directory but that doesn’t mean you wont find this file elsewhere. If you stumble across this file make sure to look for sensitive information such as usernames, passwords, and database credentials.
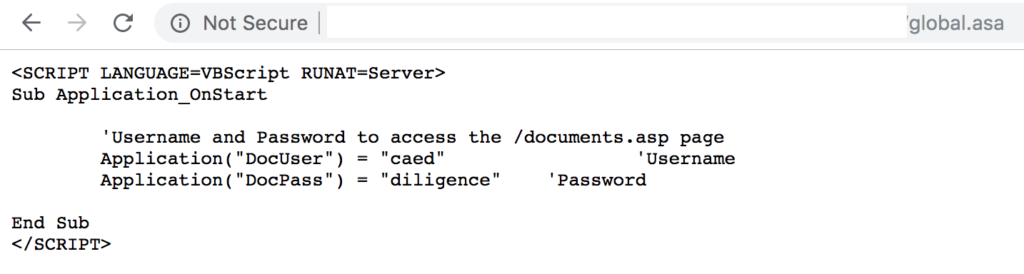
As you can see the above example contains a username with its associated password. Note that this file was not found on the root directory which is where I normally find these.
Larvel Framework
Larvel is a fairly popular PHP framework. This framework stores its logs files at “/storage/logs/laravel.log” which is accessible by anyone.
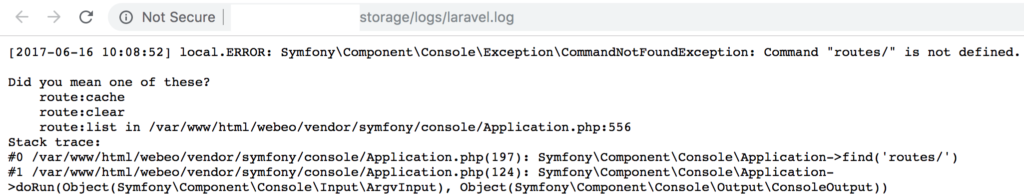
This file can contain all kinds of hidden gems. You can find usernames, passwords, environment variables and more.
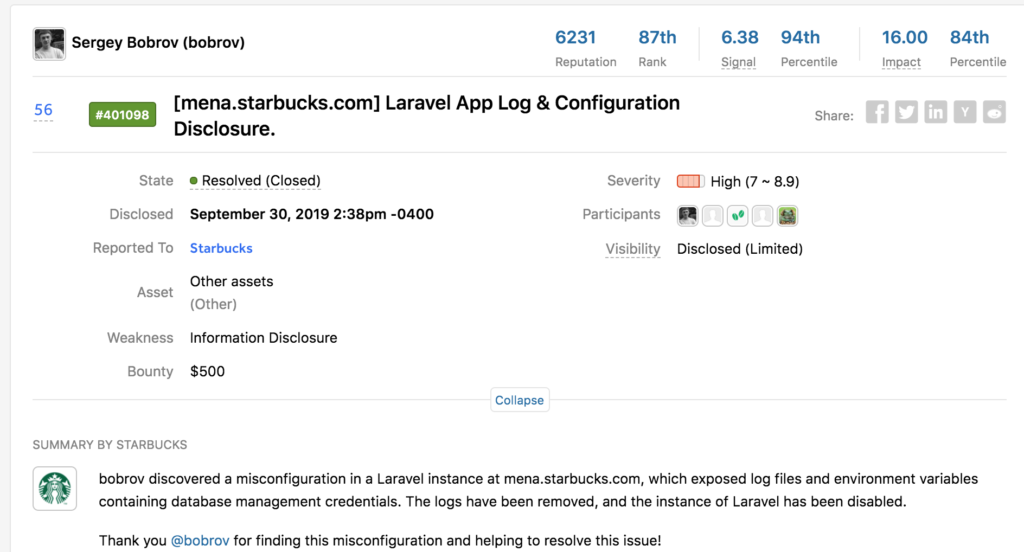
Looks like Starbucks paid $500 because someone found database credentials in this log file. Thats $500 dollars for something that probably took 60 seconds to find. That could easily be you.
Zend Framework
This is another framework that stores sensitive information in its configuration files. The “/application/configs/application.ini” file is used to store database credentials.
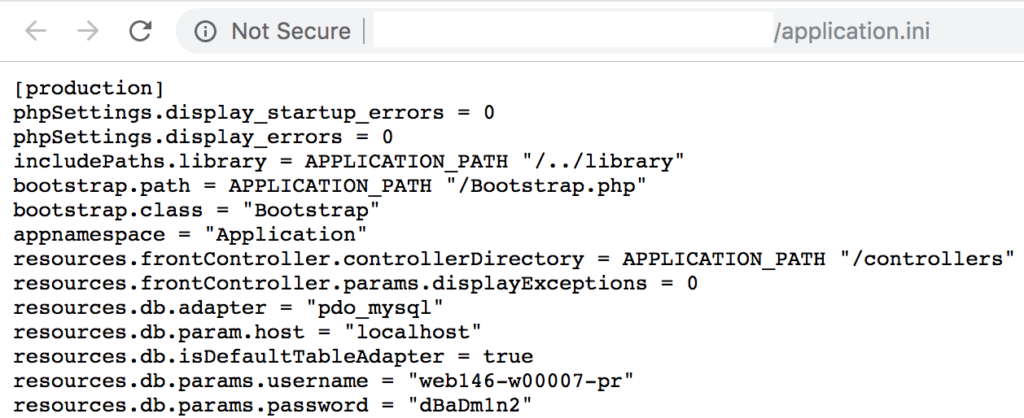
This file is not exposed by default but developers often mess things up and exposed this file by accident.
Conclusion
Finding exposed log and configuration files is one of the easiest ways to find credentials and other sensitive information. You can create a list of possible file names such as log.txt but most frameworks use a unique name. The only way to find these file names is to understand the framework and how it names its log or configuration files. This comes with experience and exposure to different technology stacks.
I have not checked in here for some time because I thought it was getting boring, but the last several posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
I intended to write you the very small observation in order to give many thanks over again relating to the magnificent tips you’ve provided in this case. It was so shockingly generous with you to give extensively what a lot of people could possibly have sold as an e book to generate some cash for themselves, specifically now that you might well have tried it in case you considered necessary. Those creative ideas in addition acted as a fantastic way to fully grasp the rest have similar dream the same as my personal own to see a whole lot more on the subject of this problem. I know there are some more pleasant instances up front for those who read your site.