Slack Group
Before we get started I have started a slack group dedicated to hacking. We welcome everyone from beginner to advanced to join. I will be on everyday answer questions, doing CTFs, and talking about cool hacks. If you enjoy hacking and are looking for like minded people join below:
NEW Hacking Group Slack Channel
Introduction
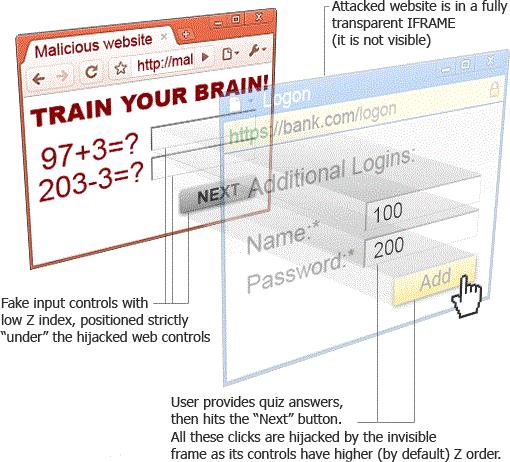
According to Google clickjacking is a malicious technique of tricking a user into clicking on something different from what the user perceives, thus potentially revealing confidential information or allowing others to take control of their computer while clicking on seemingly innocuous objects, including web pages.
Clickjacking
Clickjacking occurs when a third party website is able to load a target domain in an Iframe. An IFrame (Inline Frame) is an HTML document embedded inside another HTML document on a website. Basically it allows us to load a target domain within our site. If the victim is authenticated to the target site in another tab then we will also be authenticated in the iframe even if its loaded by a third party domain.
So lets say we are logged into a banking application. If the site is vulnerable to click jacking we should be able to load this application in an Iframe. An attacker could abuse this functionality by making the Iframe transparent and tricking us into performing some unwanted action such as disabling our account, liking a page, or transferring money.
This vulnerability is extremely easy to test for. All you have to do is verify that you can load the target site in an Iframe. If you can then they are vulnerable to clickjacking.
<html>
<head>
<title>Clickjacking test page</title>
</head>
<body>
<p>Website is vulnerable to clickjacking</p>
<iframe src="http://www.example-bank.com/" width="500" height="500"></iframe>
</body>
</html>Note that just because a site is vulnerable doesn’t mean it’s impactful. For example if you have a click jacking vulnerability on the login page of a site can a hacker actually do something with this? Probably not. However, if you have clickjacking on a banking form that allows you to transfer money you might be able to do something useful with that. Im saying this so you don’t go around claiming a bunch of sites are vulnerable to clickjacking when it doesn’t even matter because it has no impact.
X-frame Options
The X-frame options header was created to help thwart this type of attack by limiting which domains can load it in an iframe.
| Deny | Blocks all domains from loading in an iframe |
| Same Origin | An iframe can only be loaded by the current domain(itself). No other domains. |
| Allow-From URI | Only the specified domain can load the this domain in an iframe |
If you see any of those X-frame values the site most likely isn’t vulnerable to clickjacking but its still worth checking. Note that the X-frame header is being phased out and may not be supported by all browsers.
Content Security Policy (CSP)
The Content Security Policy (CSP) is a computer security standard introduced to prevent cross-site scripting, clickjacking and other code injection attacks resulting from execution of malicious content in the trusted web page context. Previously I mentioned the X-frame header is being phased out, this will eventually be replaced by the CSP.
The frame-ancestors directive can be used to prevent clickjacking by limiting which domains can load an iframe.
| Content-Security-Policy: frame-ancestors ‘none’; | Blocks all domains from loading in an iframe |
| Content-Security-Policy: frame-ancestors ‘self’; | An iframe can only be loaded by the current domain(itself). No other domains. |
| Content-Security-Policy: frame-ancestors ‘self’ https://example.com; | Only the specified domain can load the this domain in an iframe |
If you see any of those frame-ancestor values the site is most likely not vulnerable to clickjacking but its still worth checking.
Note that the CSP frame-ancestors is still being rolled out and is not supported by all the major browsers yet.
Conclusion
Clickjacking is a fairly low impact vulnerability but under the right circumstances it can have a huge impact. If you’r able to load a target site in an Iframe they are vulnerable to clickjacking. However, you should always verify that you can do something impactful with the vulnerability before mentioning it.